This is part two of a series of posts that contain key excerpts of my paper, Using Sysmon to Enrich Security Onion’s Host-Level Capabilities.
Unfortunately, it is not just encrypted traffic that harries NSM practitioners – the persistence of advanced adversaries continues unabated. This has given rise to intelligence-driven CND, which is a threat-centric risk management strategy. (Hutchins, Cloppert, & Amin) Simply put, as the defender gathers intelligence about intrusions and the adversary behind them, the defender is able to use this information in future detection cycles against the adversary. Indicators are a key part of this intelligence. From the formative paper, Intelligence-Driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chains: “By completely understanding an intrusion, and leveraging intelligence on these tools and infrastructure, defenders force an adversary to change every phase of their intrusion in order to successfully achieve their goals in subsequent intrusions. In this way, network defenders use the persistence of adversaries’ intrusions against them to achieve a level of resilience.” (Hutchins, Cloppert, & Amin)
A crucial part of this methodology is the ability to gather quality indicators. Quality indicators are extractable (“Can I find this indicator in my data?”), purposeful (“To what use will I put this indicator?”), and actionable (“If I find this indicator in my data, can I do something with that information?”). (Bianco, Enterprise Security Monitoring, 2013) Without these quality indicators, defenders will not be able to efficiently detect further intrusions by the same adversary. Various forms of indicators have differing values. Consider David Bianco’s Pyramid of Pain:
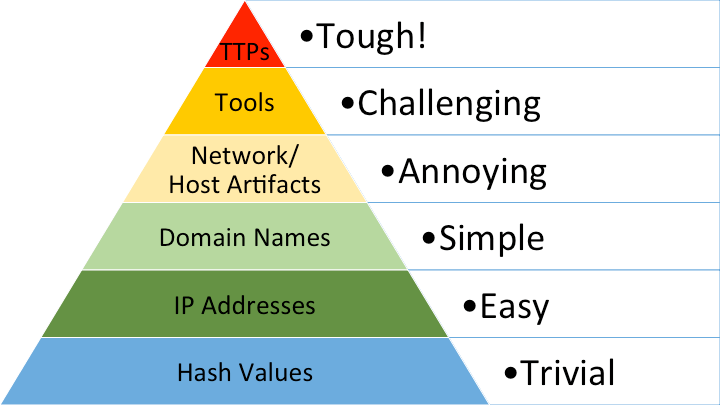
It can be seen that Hash Values and IP Addresses are on the bottom of the pyramid. This indicates that though these types of indicators can be useful, they are very easy for the adversary to cycle through, hence the probability of seeing the same indicator used in multiple campaigns is much lower than tools that the adversary uses (which is much higher on the pyramid). The key point is that as the defender is able to build up their detection strategy around higher quality indicators, this will require the adversary to change their Tools, Tactics, and Procedures (TTPs), which is very costly in terms of time and resources. This does not negate the fact that the lower indicator types are still useful.
Though there are different types of indicators (Atomic, Computed and Behavioral), it is clear that the defender must have indicators that span the gamut of both network and host-level, as an adversary carries out operations in both spaces. (Hutchins, Cloppert, & Amin)
References
Hutchins, E. M., Cloppert, M. J., & Amin, R. M. (n.d.). Intelligence-Driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chains. Retrieved February 12, 2015, from lockheedmartin.com: http://www.lockheedmartin.com/content/dam/lockheed/data/corporate/documents/LM-White-Paper-Intel-Driven-Defense.pdf
Bianco, D. (2013, September 14). Enterprise Security Monitoring. Retrieved February 12, 2015, from speakerdeck.com: https://speakerdeck.com/davidjbianco/enterprise-security-monitoring
Bianco, D. (2014, January 17). The Pyramid of Pain. Retrieved from Enterprise Detection and Response: http://detect-respond.blogspot.com/2013/03/the-pyramid-of-pain.html